Microsoft has officially extended the retirement of the Azure‑based Sentinel experience to March 31, 2027, giving organisations nearly a year more than originally planned to shift fully into the Microsoft Defender portal. This move comes after significant customer and partner feedback, especially from those managing Sentinel at scale, who stressed the need for additional time and capability maturity before committing to a full transition.
As a cloud architect working with customers navigating operational change, I actually see this announcement as more than just “more time.” It reflects the scale of transformation Microsoft is driving, moving Sentinel from a standalone SIEM experience toward a unified SecOps fabric where SIEM and XDR finally live side-by-side.
Why This Matters: The Portal Is Becoming the Platform
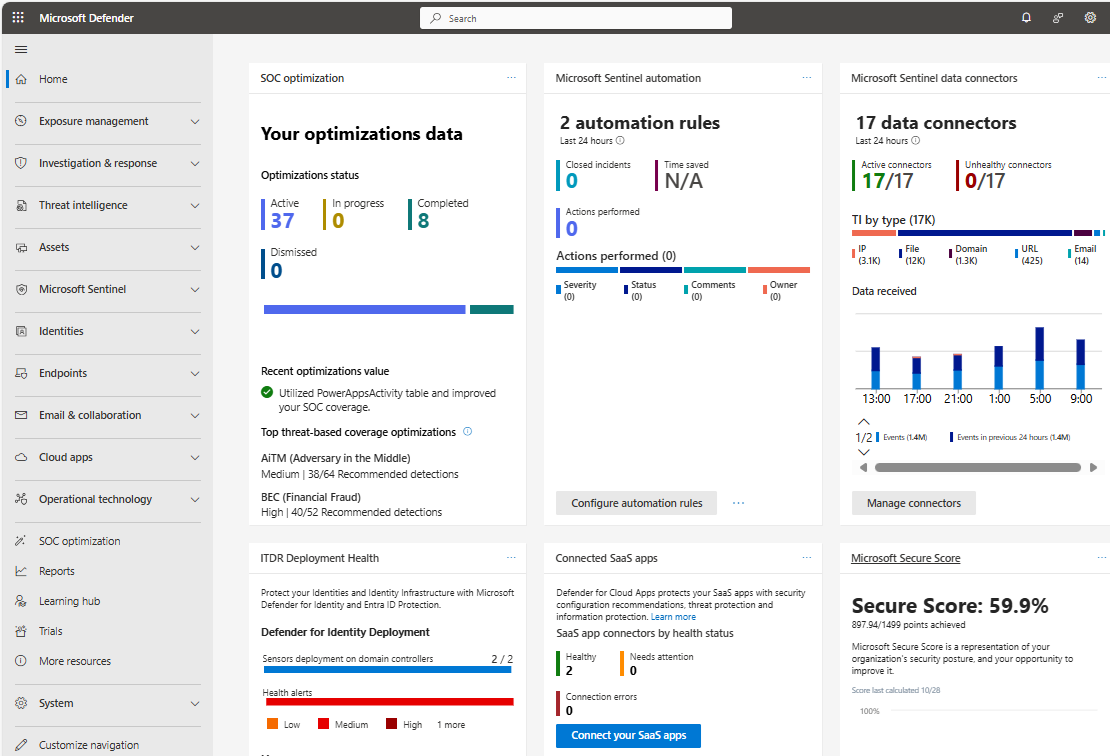
The Defender portal is far more than a refreshed UI. Microsoft is unifying the full capabilities of Microsoft Sentinel, Microsoft Defender XDR, Microsoft Security Exposure Management, and generative AI into a single operational hub for its security ecosystem.
Several capabilities now exist exclusively within this portal, including:
- Security Copilot, Microsoft’s GenAI-driven assistant for incident response and threat hunting.
- Sentinel Data Lake for long-term security data retention and advanced analytics.
- Sentinel Graph, a unified intelligence layer mapping relationships across entities, alerts, and behaviours.
- Cross‑platform automatic attack disruption, extending beyond Azure into AWS and Proofpoint.
These capabilities show where Microsoft is investing long term. If customers stay on the Azure portal until the deadline, they’ll miss out on much of the innovation happening now.
Operational Enhancements That Shift the Migration Equation
What stood out to me most from Microsoft’s update is the steady stream of reliability and usability improvements, some of which address long‑standing partner frustrations. These include:
- Improved latency and alert reliability.
- Flexible control over incident creation.
- Updated GDAP-based multi‑tenant access for service providers.
- Incident descriptions now stored directly in the SecurityIncident table for easier API querying.
These are not cosmetic updates, they remove operational blockers that previously made large enterprises hesitant to switch portals.
Start Planning Now, Even With the Extra Time
Although the deadline has moved, delaying planning isn’t a winning strategy. With many features only available in the Defender portal, and the promise of next‑generation SOAR and case management landing there, it’s clear the Azure Sentinel interface is entering maintenance mode.
Microsoft has provided transition guides, onboarding videos, and migration‑focused webinars to help customers prepare. In my experience, organisations that start early avoid the “big‑bang migration” crunch that often strains SOC teams and interrupts daily operations.
Final Thoughts
The extension to 2027 is good news, but it shouldn’t be mistaken for a signal to pause. Microsoft’s direction is unambiguous: the Defender portal is the future home of unified security operations.
For architects, this is a prime opportunity to simplify SOC workflows, consolidate tooling, and modernise automation and data strategies. The sooner teams embrace the new experience, the sooner they unlock capabilities that simply don’t exist in the Azure portal.